- Our Story
- Publications & Resources
- Publications & Resources
- Publications
- IEEE Signal Processing Magazine
- IEEE Journal of Selected Topics in Signal Processing
- IEEE Signal Processing Letters
- IEEE/ACM Transactions on Audio Speech and Language Processing
- IEEE Transactions on Computational Imaging
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Signal and Information Processing over Networks
- IEEE Transactions on Signal Processing
- IEEE TCI
- IEEE TSIPN
- Data & Challenges
- Submit Manuscript
- Guidelines
- Information for Authors
- Special Issue Deadlines
- Overview Articles
- Top Accessed Articles
- SPS Newsletter
- SigPort
- SPS Resource Center
- Publications Feedback
- Publications FAQ
- Blog
- News
- Dataset Papers
- Conferences & Events
- Community & Involvement
- Professional Development
- For Volunteers
- Information for Authors-OJSP
-
Home
Conferences Events IEEE JSTSP Article IEEE Signal Processing Magazine IEEE TIFS Article IEEE TMM Article IEEE TSP Article Jobs in Signal Processing Lectures Machine Learning Seasonal Schools Signal Processing News SPM Article SPS Distinguished Lectures SPS Newsletter Article SPS Webinar SPS Webinars SPS Webinar Series Webinar webinars
-
Our Story
What is Signal Processing?
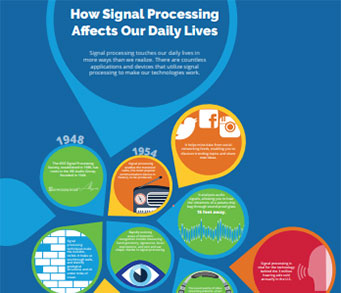
The technology we use, and even rely on, in our everyday lives –computers, radios, video, cell phones – is enabled by signal processing. Learn More » -
Publications & Resources
-
SPS Resources
- Signal Processing Magazine The premier publication of the society.
- SPS Newsletter Monthly updates in Signal Processing
- SPS Resource Center Online library of tutorials, lectures, and presentations.
- SigPort Online repository for reports, papers, and more.
- SPS Feed The latest news, events, and more from the world of Signal Processing.
-
SPS Resources
-
Conferences & Events
-
Community & Involvement
-
Membership
- Join SPS The IEEE Signal Processing Magazine, Conference, Discounts, Awards, Collaborations, and more!
- Chapter Locator Find your local chapter and connect with fellow industry professionals, academics and students
- Women in Signal Processing Networking and engagement opportunities for women across signal processing disciplines
- Students Scholarships, conference discounts, travel grants, SP Cup, VIP Cup, 5-MICC
- Young Professionals Career development opportunities, networking
- Get Involved
-
Technical Committees
- Applied Signal Processing Systems
- Audio and Acoustic Signal Processing
- Bio Imaging and Signal Processing
- Computational Imaging
- Image Video and Multidimensional Signal Processing
- Information Forensics and Security
- Machine Learning for Signal Processing
- Multimedia Signal Processing
- Sensor Array and Multichannel
- Signal Processing for Communication and Networking
- Signal Processing Theory and Methods
- Speech and Language Processing
- Technical Working Groups
- More TC Resources
-
Membership
-
Professional Development
-
Professional Development
- Mentoring Experiences for Underrepresented Young Researchers (ME-UYR)
- Micro Mentoring Experience Program (MiME)
- Distinguished Lecturer Program
- Distinguished Lecturers
- Distinguished Lecturer Nominations
- Past Lecturers
- Distinguished Industry Speaker Program
- Distinguished Industry Speakers
- Distinguished Industry Speaker Nominations
- Industry Resources
- IEEE Training Materials
- Jobs in Signal Processing: IEEE Job Site
-
Career Resources
- SPS Education Program Educational content in signal processing and related fields.
- Distinguished Lecturer Program Chapters have access to educators and authors in the fields of Signal Processing
- PROGRESS Initiative Promoting diversity in the field of signal processing.
- Job Opportunities Signal Processing and Technical Committee specific job opportunities
- Job Submission Form Employers may submit opportunities in the area of Signal Processing.
-
Professional Development
-
For Volunteers
-
For Board & Committee Members
- Board Agenda/Minutes* Agendas, minutes and supporting documentation for Board and Committee Members
- SPS Directory* Directory of volunteers, society and division directory for Board and Committee Members.
- Membership Development Reports* Insight into the Society’s month-over-month and year-over-year growths and declines for Board and Committee Members
-
For Board & Committee Members
Popular Pages
Today's:
- Submit a Manuscript
- Information for Authors
- (MLSP 2024) 2024 IEEE International Workshop on Machine Learning for Signal Processing
- IEEE Transactions on Multimedia
- Award Recipients
- Board of Governors
- Signal Processing Cup
- IEEE Transactions on Image Processing
- IEEE/ACM Transactions on Audio Speech and Language Processing
- (SLT 2024) 2024 IEEE Spoken Language Technology Workshop
- IEEE Transactions on Information Forensics and Security
- Conferences & Events
- (ICASSP 2025) 2025 IEEE International Conference on Acoustics, Speech and Signal Processing
- SPS Scholarship Program
- Conference Call for Papers
All time:
- Information for Authors
- Submit a Manuscript
- IEEE Transactions on Image Processing
- 404 Page
- IEEE/ACM Transactions on Audio Speech and Language Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Signal Processing Letters
- IEEE Transactions on Signal Processing
- Conferences & Events
- IEEE Journal of Selected Topics in Signal Processing
- Information for Authors-SPL
- Conference Call for Papers
- Signal Processing 101
- IEEE Signal Processing Magazine
Last viewed:
- (ICME 2024) 2024 IEEE International Conference on Multimedia and Expo
- Submit a Manuscript
- IEEE TCI Special Section on Computational Imaging using Synthetic Apertures
- IEEE Transactions on Multimedia
- IEEE JSTSP Special Series on AI in Signal & Data Science - Toward Explainable, Reliable, and Sustainable Machine Learning
- Conference Call for Papers
- IEEE SPM Special Issue on Near-Field Signal Processing: Communications, Sensing and Imaging
- IEEE Journal of Selected Topics in Signal Processing
- Membership
- Video & Image Processing Cup
- Board of Governors
- Executive Committee
- ICASSP 2024 Speech Signal Improvement Challenge: ICASSP 2024
- (WIFS 2024) 2024 IEEE International Workshop on Information Forensics and Security
- IEEE Transactions on Image Processing
Newsletter Menu
Newsletter Categories
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
News and Resources for Members of the IEEE Signal Processing Society
Recent PhD theses
Perreault, Logan Jared. (Montana State University) “On the Usability of Continuous Time Bayesian Networks: Improving Scalability and Expressiveness” (2017), Advisor: Sheppard, John W., https://www.cs.montana.edu/sheppard/
The Continuous Time Bayesian Network (CTBN) is a model capable of compactly representing the behavior of discrete state systems that evolve in continuous time. This is achieved by factoring a Continuous Time Markov Process using the structure of a directed graph. Although CTBNs have proven themselves useful in a variety of applications, adoption of the model for use in real-world problems can be difficult. The authors believe this is due in part to limitations relating to scalability as well as representational power and ease of use. This dissertation attempts to address these issues.
First, the authors improve the expressiveness of CTBNs by providing procedures that support the representation of non-exponential parametric distributions. The authors also propose the Continuous Time Decision Network (CTDN) as a framework for representing decision problems using CTBNs. This new model supports optimization of a utility value as a function of a set of possible decisions. Next, the authors address the issue of scalability by providing two distinct methods for compactly representing CTBNs by taking advantage of similarities in the model parameters. These compact representations are able to mitigate the exponential growth in parameters that CTBNs exhibit, allowing for the representation of more complex processes. The authors then introduce another approach to managing CTBN model complexity by introducing the concept of disjunctive interaction for CTBNs. Disjunctive interaction has been used in Bayesian networks to provide significant reductions in the number of parameters, and the authors have adapted this concept to provide the same benefits within the CTBN framework.
Finally, the authors demonstrate how CTBNs can be applied to the real-world task of system prognostics and diagnostics. The authors show how models can be built and parameterized directly using information that is readily available for diagnostic models. The authors then apply these model construction techniques to build a CTBN describing a vehicle system. The vehicle model makes use of some of the newly introduced algorithms and techniques, including the CTDN framework and disjunctive interaction. This extended application not only demonstrates the utility of the novel contributions presented in this work, but also serves as a template for applying CTBNs to other real-world problems.
Aditham, Santosh. University of South Florida, “Mitigation of Insider Attacks for Data Security in Distributed Computing Environments” (2017), Advisor: Ranganathan, Nagarajan http://www.usf.edu/engineering/cse/people/ranganathan-nagarajan.aspx and Katkoori, Srinivas http://www.usf.edu/engineering/cse/people/katkoori-srinivas.aspx
In big data systems, the infrastructure is such that large amounts of data are hosted away from the users. Information security is a major challenge in such systems. From the customer’s perspective, one of the big risks in adopting big data systems is in trusting the service provider who designs and owns the infrastructure, with data security and privacy. However, big data frameworks typically focus on performance and the opportunity for including enhanced security measures is limited. In this dissertation, the problem of mitigating insider attacks is extensively investigated and several static and dynamic run-time techniques are developed. The proposed techniques are targeted at big data systems but applicable to any data system in general. First, a framework is developed to host the proposed security techniques and integrate with the underlying distributed computing environment. The authors endorse the idea of deploying this framework on special purpose hardware and a basic model of the software architecture for such security coprocessors is presented. Then, a set of compile-time and run-time techniques are proposed to protect user data from the perpetrators. These techniques target detection of insider attacks that exploit data and infrastructure. The compile-time intrusion detection techniques analyze the control flow by disassembling program binaries while the run-time techniques analyze the memory access patterns of processes running on the system. The proposed techniques have been implemented as prototypes and extensively tested using big data applications. Experiments were conducted on big data frameworks such as Hadoop and Spark using cloud-based services. Experimental results indicate that the proposed techniques successfully detect insider attacks in the context of data loss, data degradation, data exposure and infrastructure degradation.
Steinemann, Natalie Anna. The City College of New York, “Perceptual decision making in humans: Neural correlates along the sensorimotor hierarchy” (2017) Advisor: Kelly, Simon P. https://www.gc.cuny.edu/Page-Elements/Academics-Research-Centers-Initiat...
Decision-making has been studied in a variety of fields ranging from economics to computer science. Within the neural sciences, a perceptual decision has been defined as the translation of sensory perception into goal-directed actions. Great strides have been achieved in uncovering the neural underpinnings of decision-making primarily through single-unit recordings in non-human primates. The results of these studies suggest that decisions are computed in neural populations specific to the effector employed to report the outcome of the decision. Results obtained by non-invasive measures in humans, on the other hand, indicate that a supra-modal decision area may exist, which drives the activity observed in effector-specific neural populations. Due to differences in the scale of measurement, it has, however, been challenging to translate these groundbreaking findings to the human brain where data recordings are commonly limited to non-invasive electrophysiology and neuroimaging.
The research summarized in this dissertation was designed to gain a more complete understanding of the functional significance of decision correlates measured non-invasively in humans. The authors first characterize non-invasively measured signals of sensory representation, decision formation, motor preparation, and response execution, and give new insight into the differential influence of evidence and response time constraints all of these key stages. In line with previous reports in human and non-human primates, the authors found response time constraints to have a substantial effect on signatures of motor preparation before the onset of sensory evidence as well as during evidence evaluation. Additionally, the authors found that response time constraints enhance the differential representation of sensory evidence and accelerate the process of motor response execution. In a second study, the authors use neuroimaging to localize potential sources of effector-independent evidence accumulation in the human brain. Neural populations in the supramarginal gyrus of the parietal lobe, right operculum, left insula, and left inferior frontal gyrus are identified as candidate regions. Among the four regions, it is suggested that the neural population in supramarginal gyrus may be situated upstream of the other three in the sensorimotor hierarchy. Finally, the authors identify the means by which non-invasive decision correlates measured in humans may advance the understanding of other cognitive processes such as memory formation and aid in the diagnosis of learning disorders.
Wang, Panqu. University of California, San Diego, “Towards The Deep Model: Understanding Visual Recognition Through Computational Models”, (2017), Advisor: Cottrell, Garrison https://cseweb.ucsd.edu/~gary/ and Vasconcelos, Nuno http://www.svcl.ucsd.edu/~nuno/
Understanding how visual recognition is achieved in the human brain is one of the most fundamental questions in vision research. In this thesis the authors seek to tackle this problem from a neurocomputational modeling perspective. More specifically, the authors build machine learning-based models to simulate and explain cognitive phenomena related to human visual recognition, and the authors improve computational models using brain-inspired principles to excel at computer vision tasks. The authors first describe how a neurocomputational model (“The Model”, TM, (Cottrell & Hsiao, 2011)) can be applied to explain the modulation of visual experience on the performance of subordinate-level face and object recognition. Next, by introducing a mixture-of-experts structure in the model, the authors show that TM can be used to simulate the development of hemispheric lateralization of face processing. In addition, the authors extend TM to “The Deep Model” (TDM) by coupling it with deep learning techniques, and use TDM to explain the peripheral vision advantage in human scene recognition. Furthermore, the authors show the performance of these computational methods can be improved by introducing realistic constraints based on the human brain. By combining unsupervised feature learning principles with the Gnostic Fields theory of how the brain performs object recognition across the ventral visual pathway, the authors show a biologically-inspired model can develop realistic features of the early visual cortex, while performing well on object recognition datasets. By designing better encoding and decoding strategies in the deep neural network, the authors demonstrate that their system achieves the state-of-the-art performance on pixel-level semantic segmentation task on many popular computer vision benchmarks.
Open Calls
Conference News
Education & Resources
Society News
- Introducing the NEW Women in Signal Processing Directory!
- Job Opportunities in Signal Processing
- Upcoming Distinguished Lectures
- IEEE SPS and TELUS Take Off with New Video on Air Canada Flights
- Meet the Candidates: 2018 IEEE President-Elect and IEEE Technical Activities Vice President-Elect
- Election of Regional Directors-at-Large and Members-at-Large
Chapter & DL News
Initiatives & Trends
SPS on Twitter
- DEADLINE EXTENDED: The 2023 IEEE International Workshop on Machine Learning for Signal Processing is now accepting… https://t.co/NLH2u19a3y
- ONE MONTH OUT! We are celebrating the inaugural SPS Day on 2 June, honoring the date the Society was established in… https://t.co/V6Z3wKGK1O
- The new SPS Scholarship Program welcomes applications from students interested in pursuing signal processing educat… https://t.co/0aYPMDSWDj
- CALL FOR PAPERS: The IEEE Journal of Selected Topics in Signal Processing is now seeking submissions for a Special… https://t.co/NPCGrSjQbh
- Test your knowledge of signal processing history with our April trivia! Our 75th anniversary celebration continues:… https://t.co/4xal7voFER
Home | Sitemap | Contact | Accessibility | Nondiscrimination Policy | IEEE Ethics Reporting | IEEE Privacy Policy | Terms | Feedback
© Copyright 2024 IEEE – All rights reserved. Use of this website signifies your agreement to the IEEE Terms and Conditions.
A not-for-profit organization, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity.