SPS Feed
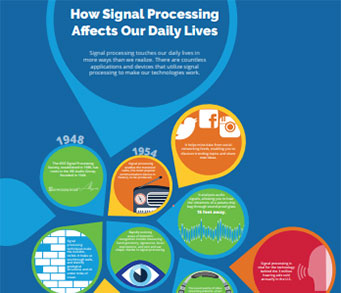
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
The Latest News, Articles, and Events in Signal Processing
Submission Deadline: March 2, 2020
Call for Proposals Document
Lecture Date: April 10, 2020
Chapter: Malaysia
Chapter Chair: R. Logeswaran
Topics: When blockchain meets computer vision: Opportunities and challenges
The 27th European Signal Processing Conference (EUSIPCO) was held 2–6 September 2019 at the A Coruña Conference Center, Palexco. “Balcony of the Atlantic,” “Crystal City,” and “Herculine City” are some of the nicknames for A Coruña, Spain, whose motto is “A Coruña, a cidade onde ninguén é forasteiro,” which translates into “A Coruña, the city where nobody is an outsider.”
The articles in this special section focus on computational magnetic resonance imaging (MRI) using compressed sensing applications. Presents recent developments in computational MRI. These developments are pushing the frontier of computational imaging beyond CS. Similar to CS, most of these algorithms rely on image representation in one form or another.
I have made a concerted effort in my previous editorials to cover topics that embrace our humanity and diversity and touch on issues of social value, the environment, the universe, our history, and science. In it all, I hope that you were able to see the reach and impact of our discipline into the depths of our existence.
In an increasingly networked world, signal processing is leading the way to innovations that promise to raise data throughput and capacity to levels scarcely dreamed of a decade ago.
Since its inception in the early 1970s [1], magnetic resonance imaging (MRI) has revolutionized radiology and medicine. Apart from high-quality data acquisition, image reconstruction is an important step to guarantee high image quality in MRI.
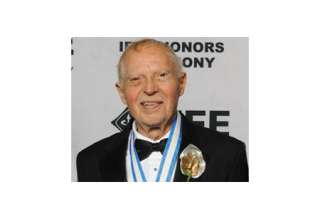
IEEE Life Fellow James J. Spilker, Jr., Global Positioning Systems (GPS) pioneer, philanthropist, and entrepreneur died on 24 September at the age of 86. Lives around the world are better every day thanks to Prof. Spilker’s passion and dedication to his work. Prof. Spilker’s early childhood was marked by difficulties.
This paper proposes nonorthogonal sharing of available resources between latency-critical and latency-tolerant communication for fulfilling tight requirements of ultrareliable low-latency communication (URLLC) as well as avoiding inefficient spectrum utilization of grant-based (GB) access for sporadic URLLC traffic.

Ph.D. positions with full financial support are now available in Dr. Ying Liu’s group in the Department of Computer Science and Engineering at Santa Clara University (SCU). Dr. Liu is looking for self-motivated PhD students to work on image/video processing, machine learning and deep learning.

- Tackle challenges in data collection, information extraction & transmission.
- Excellent opportunity to work in a leading scientific institution with dedicated professionals
- Join CSIRO’s Data61, the largest data innovation group in Australia
The Position

DSP/FPGA Engineer (Mid-to-Senior Level Position)
Are you seeking a truly creative, challenging technical opportunity? Does product development excite you more than filling out a timecard? Does working in a tightly integrated hardware and software team where thinking outside the box is rewarded sound exciting? Do you want to be a part of a high visibility effort to create a next-generation Counter UAS (C-UAS) system and get paid to work with drones?
Lecture Date: March 3, 2020
Chapter: Western Puerto Rico
Chapter Chair: Rogelio Palomera-Garcia
Topics: Imaging Arithmetic: Physics U Math + Math
Manuscript Due: August 1, 2020
Publication Date: April 2021
CFP Document
Pages
SPS Social Media
- IEEE SPS Facebook Page https://www.facebook.com/ieeeSPS
- IEEE SPS X Page https://x.com/IEEEsps
- IEEE SPS Instagram Page https://www.instagram.com/ieeesps/?hl=en
- IEEE SPS LinkedIn Page https://www.linkedin.com/company/ieeesps/
- IEEE SPS YouTube Channel https://www.youtube.com/ieeeSPS