- Our Story
- Publications & Resources
- Publications & Resources
- Publications
- IEEE Signal Processing Magazine
- IEEE Journal of Selected Topics in Signal Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Computational Imaging
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Signal and Information Processing over Networks
- IEEE Transactions on Signal Processing
- IEEE TCI
- IEEE TSIPN
- Data & Challenges
- Submit Manuscript
- Guidelines
- Information for Authors
- Special Issue Deadlines
- Overview Articles
- Top Accessed Articles
- SPS Newsletter
- SigPort
- SPS Resource Center
- Publications FAQ
- Blog
- News
- Dataset Papers
- Conferences & Events
- Community & Involvement
- Professional Development
- For Volunteers
- Information for Authors-OJSP
-
Home
Conferences Events IEEE Signal Processing Magazine IEEE SPL Article IEEE TIFS Article IEEE TMM Article IEEE TSP Article Jobs in Signal Processing Lectures Machine Learning Seasonal Schools Signal Processing News SPM Article SPS Distinguished Lectures SPS Newsletter Article SPS Webinar SPS Webinars SPS Webinar Series Webinar webinars
-
Our Story
What is Signal Processing?
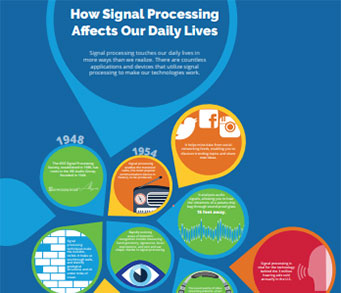
The technology we use, and even rely on, in our everyday lives –computers, radios, video, cell phones – is enabled by signal processing. Learn More » -
Publications & Resources
-
SPS Resources
- Signal Processing Magazine The premier publication of the society.
- SPS Newsletter Monthly updates in Signal Processing
- SPS Resource Center Online library of tutorials, lectures, and presentations.
- SigPort Online repository for reports, papers, and more.
- SPS Feed The latest news, events, and more from the world of Signal Processing.
-
SPS Resources
-
Conferences & Events
-
Community & Involvement
-
Membership
- Join SPS The IEEE Signal Processing Magazine, Conference, Discounts, Awards, Collaborations, and more!
- Chapter Locator Find your local chapter and connect with fellow industry professionals, academics and students
- Women in Signal Processing Networking and engagement opportunities for women across signal processing disciplines
- Students Scholarships, conference discounts, travel grants, SP Cup, VIP Cup, 5-MICC
- Young Professionals Career development opportunities, networking
- Get Involved
-
Technical Committees
- Applied Signal Processing Systems
- Audio and Acoustic Signal Processing
- Bio Imaging and Signal Processing
- Computational Imaging
- Image Video and Multidimensional Signal Processing
- Information Forensics and Security
- Machine Learning for Signal Processing
- Multimedia Signal Processing
- Sensor Array and Multichannel
- Signal Processing for Communication and Networking
- Signal Processing Theory and Methods
- Speech and Language Processing
- Technical Working Groups
- More TC Resources
-
Membership
-
Professional Development
-
Professional Development
- Signal Processing Mentorship Academy (SigMA) Program
- Micro Mentoring Experience Program (MiME)
- Distinguished Lecturer Program
- Distinguished Lecturers
- Distinguished Lecturer Nominations
- Past Lecturers
- Distinguished Industry Speaker Program
- Distinguished Industry Speakers
- Distinguished Industry Speaker Nominations
- Industry Resources
- IEEE Training Materials
- Jobs in Signal Processing: IEEE Job Site
-
Career Resources
- SPS Education Program Educational content in signal processing and related fields.
- Distinguished Lecturer Program Chapters have access to educators and authors in the fields of Signal Processing
- Job Opportunities Signal Processing and Technical Committee specific job opportunities
- Job Submission Form Employers may submit opportunities in the area of Signal Processing.
-
Professional Development
-
For Volunteers
-
For Board & Committee Members
- Board Agenda/Minutes* Agendas, minutes and supporting documentation for Board and Committee Members
- SPS Directory* Directory of volunteers, society and division directory for Board and Committee Members.
- Membership Development Reports* Insight into the Society’s month-over-month and year-over-year growths and declines for Board and Committee Members
-
For Board & Committee Members
Popular Pages
Today's:
- Information for Authors
- Information for Authors OJSP
- IEEE Open Journal of Signal Processing
- (ICME 2026) 2026 IEEE International Conference on Multimedia and Expo
- Access Restricted
- (ASRU 2025) 2025 IEEE Automatic Speech Recognition and Understanding Workshop
- Publications
- Publications & Resources
- SPS Scholarship Program
- Guidelines
- Author Instructions For OJSP Reproducibility Review
- IEEE Journal of Selected Topics in Signal Processing
- Submit a Manuscript
- Conference Call for Papers
- Model-Driven Deep Learning for MIMO Detection
All time:
- Information for Authors
- Submit a Manuscript
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Audio, Speech and Language Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Signal Processing
- Conferences & Events
- IEEE Journal of Selected Topics in Signal Processing
- Information for Authors-SPL
- Conference Call for Papers
- Signal Processing 101
- IEEE Signal Processing Magazine
- Guidelines
Last viewed:
- IEEE Open Journal of Signal Processing
- Call for Proposals: IEEE ICME 2026
- Publications & Resources
- 100 Signal Processing Society Members Elevated to Senior Member!
- (ICASSP 2022) 2022 IEEE International Conference on Acoustics, Speech and Signal Processing
- (ICME 2026) 2026 IEEE International Conference on Multimedia and Expo
- Conference Call for Papers
- Meet SPS Member Ahmet Mete Elbir
- (ICIP 2025) 2025 IEEE International Conference on Image Processing
- (ICASSP 2026) 2026 IEEE International Conference on Acoustics, Speech, and Signal Processing
- Video of the month: What is Signal Processing?
- Conferences & Events
- Industry Resources
- Information for Authors
- Information for Authors-SPM
Alturkostani, Hani Eftikhar (University of Idaho), “Mitigation Strategies for Safety Applications in Vehicular Ad Hoc Networks Subjected to Jamming” (2016)
You are here
Newsletter Menu
Newsletter Categories
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
News and Resources for Members of the IEEE Signal Processing Society
Alturkostani, Hani Eftikhar (University of Idaho), “Mitigation Strategies for Safety Applications in Vehicular Ad Hoc Networks Subjected to Jamming” (2016)
Alturkostani, Hani Eftikhar (University of Idaho), “Mitigation Strategies for Safety Applications in Vehicular Ad Hoc Networks Subjected to Jamming” (2016) Advisor: Krings, Axel
The term Intelligent Transportation Systems (ITS) refers to the technologies, services, and applications that allow vehicles to communicate with each other (V2V) and also with fixed infrastructures (V2I) and (I2V). This collaborative communication forms a Vehicular Ad-Hoc Network (VANET) that enables the deployment of a wide range of useful applications to address some of transportation’s most critical elements, such as mobility, environment, and safety. A key technology to facilitate such communication is called Dedicated Short Range Communications (DSRC), which operates in the 5.9 GHz band. One of the most important applications in ITS, furthermore, are DSRC Safety Applications, which aim to enhance safety and reduce traffic accidents. The reliability of any Safety Application is crucial; any disturbance, whether benign or malicious, could lead to catastrophic consequences like injury or loss of life. Wireless jamming is considered to be a serious threat to Safety Applications due to its simple implementation and severe impact on ongoing communications. In fact, wireless jamming is capable of blocking the communication between nodes entirely and creating a Wireless Denial of Service (WDoS) attack.
In this dissertation, the authors propose a new series of mitigation strategies for DSRC Safety Applications in VANETs to enhance their overall reliability in the presence of jamming attacks. These mitigation strategies are as follows: 1) an adaptive threshold-based agreement algorithm, 2) a detection algorithm that enables jamming-aware Safety Applications, and 3) a recovery strategy that uses dynamic transmission and power rates. Throughout this dissertation, the authors discuss these mitigation strategies and investigate their usefulness using mathematical models, simulations, and field experiments. Their test results show that the mitigation strategies will help to enhance the reliability of Safety Applications in the presence of wireless jamming. In addition, the techniques recommended by this dissertation are in line with current institutional and governmental standardization efforts and will not overwhelm the communication media.
Open Calls
| Nomination/Position | Deadline |
|---|---|
| Call for proposals: 2027 IEEE Conference on Artificial Intelligence (CAI) | 1 October 2025 |
| Meet the 2025 Candidates: IEEE President-Elect | 1 October 2025 |
| Take Part in the 2025 Low-Resource Audio Codec (LRAC) Challenge | 1 October 2025 |
| Call for Nominations for the SPS Chapter of the Year Award | 15 October 2025 |
| Call for Papers for 2026 LRAC Workshop | 22 October 2025 |
| Submit a Proposal for ICASSP 2030 | 31 October 2025 |
| Call for Project Proposals: IEEE SPS SigMA Program - Signal Processing Mentorship Academy | 2 November 2025 |
Society News
- Video of the Month: SPS Members at the 2016 IEEE Honors Ceremony
- Action Required: Changes to IEEE Tagline and Related References
- IEEE Maker Project Competition: Deadline 17 September
- MGA Financial Reporting Deadline Changed to Last Day of February
- Nominations Open for 2016 Major SPS Awards
- 2017 IEEE Technical Field Award Recipients Announced
- Why Have the Governing Bodies of So Many Societies/Councils and Geographical Sections Voted to Oppose the Proposed 2016 IEEE Constitutional Amendment?
- Election of Regional Directors-at-Large and Members-at-Large
- Upcoming Distinguished Lectures
- Job Opportunities in Signal Processing
- 22 Signal Processing Society Members Elevated to Senior Member
Education & Resources
- IEEE-USA Offers Free e-books to Members in July and August
- Member Discounts: New Financial Planning Program
- Member Discounts: Learn About Risk Management
- IEEE Women in Engineering News: Leadership Summits and Events
- News from IEEE Educational Activities: New Courses Available on IEEEx.org, Publications from Standards Education and IEEE-HKN
- Call for Proposals: IEEE Humanitarian Activities Committee Project Funding in 2016: Deadline 15 August
- IEEE Smart Tech Events: Registration Open, Virtual Participation Available
Technical Committee News
Conferences & Events
SPS Social Media
- IEEE SPS Facebook Page https://www.facebook.com/ieeeSPS
- IEEE SPS X Page https://x.com/IEEEsps
- IEEE SPS Instagram Page https://www.instagram.com/ieeesps/?hl=en
- IEEE SPS LinkedIn Page https://www.linkedin.com/company/ieeesps/
- IEEE SPS YouTube Channel https://www.youtube.com/ieeeSPS
Home | Sitemap | Contact | Accessibility | Nondiscrimination Policy | IEEE Ethics Reporting | IEEE Privacy Policy | Terms | Feedback
© Copyright 2025 IEEE - All rights reserved. Use of this website signifies your agreement to the IEEE Terms and Conditions.
A public charity, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity.








