SPS Feed
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
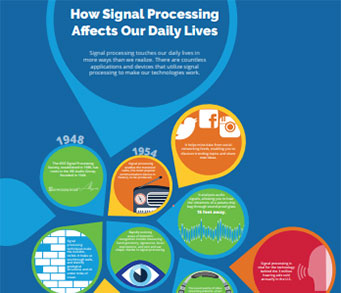
The Latest News, Articles, and Events in Signal Processing

Applying tomographic SAR inversion using compressive sensing is well established in the SAR community. In contrast to state of the art approaches applied to satellite data novel CS reconstruction approaches combining sparsity with prior information will be researched and implemented. We intend to use high resolution airborne data sets from FHR and later, from our own sensor platform. The data is superior to satellite data concerning resolution und SNR.
I am writing this column on the first official day of spring while “sheltering in place” in Northern California. In these uncertain times, we are all experiencing the anxiety that comes from an unpredictable situation that we do not control; the shock of seeing, perhaps for the first time, all of the shelves in grocery stores empty; and the stress of working, living, and sleeping in the same place.
Since the 1970s, various image and video coding techniques have been explored, and some of them have been included in the video coding standards issued by the International Organization for Standardization (ISO)/International Electrotechnical Commission (IEC) Motion Pictures Expert Group (MPEG) and International Telecommunication Union-Telecommunication Standardization Sector (ITU-T) Video Coding Experts Group (VCEG).
The current big data era routinely requires the processing of large-scale data on massive distributed computing clusters. In these applications, data sets are often so large that they cannot be housed in the memory and/or the disk of any one computer. Thus, the data and the processing are typically distributed across multiple nodes.
Batch training of machine learning models based on neural networks is well established, whereas, to date, streaming methods are largely based on linear models. To go beyond linear in the online setting, nonparametric methods are of interest due to their universality and ability to stably incorporate new information via convexity or Bayes's rule.
The field of machine learning has undergone radical transformations during the last decade. These transformations, which have been fueled by our ability to collect and generate tremendous volumes of training data and leverage massive amounts of low-cost computing power, have led to an explosion in research activity in the field by academic and industrial researchers.
Pages
SPS Social Media
- IEEE SPS Facebook Page https://www.facebook.com/ieeeSPS
- IEEE SPS X Page https://x.com/IEEEsps
- IEEE SPS Instagram Page https://www.instagram.com/ieeesps/?hl=en
- IEEE SPS LinkedIn Page https://www.linkedin.com/company/ieeesps/
- IEEE SPS YouTube Channel https://www.youtube.com/ieeeSPS