- Our Story
- Publications & Resources
- Publications & Resources
- Publications
- IEEE Signal Processing Magazine
- IEEE Journal of Selected Topics in Signal Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Computational Imaging
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Signal and Information Processing over Networks
- IEEE Transactions on Signal Processing
- IEEE TCI
- IEEE TSIPN
- Data & Challenges
- Submit Manuscript
- Guidelines
- Information for Authors
- Special Issue Deadlines
- Overview Articles
- Top Accessed Articles
- SPS Newsletter
- SigPort
- SPS Resource Center
- Publications FAQ
- Blog
- News
- Dataset Papers
- Conferences & Events
- Community & Involvement
- Professional Development
- For Volunteers
- Information for Authors-OJSP
-
Home
Waveforms for Computing Over the Air: A groundbreaking approach that redefines data aggregation
Ode to Masterfully Written Textbooks: And remembering Simon Haykin [From the Editor]
Conferences Events IEEE Signal Processing Magazine IEEE SPL Article IEEE TIFS Article IEEE TMM Article IEEE TSP Article Jobs in Signal Processing Lectures Machine Learning Seasonal Schools Signal Processing News SPM Article SPS Distinguished Lectures SPS Newsletter Article SPS Webinar SPS Webinars SPS Webinar Series Webinar webinars -
Our Story
What is Signal Processing?
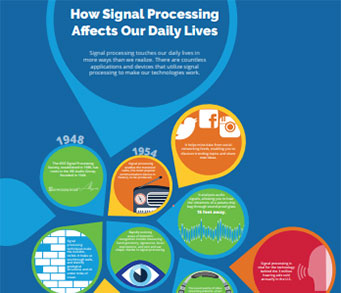
The technology we use, and even rely on, in our everyday lives –computers, radios, video, cell phones – is enabled by signal processing. Learn More » -
Publications & Resources
-
SPS Resources
- Signal Processing Magazine The premier publication of the society.
- SPS Newsletter Monthly updates in Signal Processing
- SPS Resource Center Online library of tutorials, lectures, and presentations.
- SigPort Online repository for reports, papers, and more.
- SPS Feed The latest news, events, and more from the world of Signal Processing.
-
SPS Resources
-
Conferences & Events
-
Community & Involvement
-
Membership
- Join SPS The IEEE Signal Processing Magazine, Conference, Discounts, Awards, Collaborations, and more!
- Chapter Locator Find your local chapter and connect with fellow industry professionals, academics and students
- Women in Signal Processing Networking and engagement opportunities for women across signal processing disciplines
- Students Scholarships, conference discounts, travel grants, SP Cup, VIP Cup, 5-MICC
- Young Professionals Career development opportunities, networking
- Get Involved
-
Technical Committees
- Applied Signal Processing Systems
- Audio and Acoustic Signal Processing
- Bio Imaging and Signal Processing
- Computational Imaging
- Image Video and Multidimensional Signal Processing
- Information Forensics and Security
- Machine Learning for Signal Processing
- Multimedia Signal Processing
- Sensor Array and Multichannel
- Signal Processing for Communication and Networking
- Signal Processing Theory and Methods
- Speech and Language Processing
- Technical Working Groups
- More TC Resources
-
Membership
-
Professional Development
-
Professional Development
- Signal Processing Mentorship Academy (SigMA) Program
- Micro Mentoring Experience Program (MiME)
- Distinguished Lecturer Program
- Distinguished Lecturers
- Distinguished Lecturer Nominations
- Past Lecturers
- Distinguished Industry Speaker Program
- Distinguished Industry Speakers
- Distinguished Industry Speaker Nominations
- Industry Resources
- IEEE Training Materials
- Jobs in Signal Processing: IEEE Job Site
-
Career Resources
- SPS Education Program Educational content in signal processing and related fields.
- Distinguished Lecturer Program Chapters have access to educators and authors in the fields of Signal Processing
- Job Opportunities Signal Processing and Technical Committee specific job opportunities
- Job Submission Form Employers may submit opportunities in the area of Signal Processing.
-
Professional Development
-
For Volunteers
-
For Board & Committee Members
- Board Agenda/Minutes* Agendas, minutes and supporting documentation for Board and Committee Members
- SPS Directory* Directory of volunteers, society and division directory for Board and Committee Members.
- Membership Development Reports* Insight into the Society’s month-over-month and year-over-year growths and declines for Board and Committee Members
-
For Board & Committee Members
Popular Pages
Today's:
- Information for Authors
- (ASRU 2025) 2025 IEEE Automatic Speech Recognition and Understanding Workshop
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Image Processing
- Submit a Manuscript
- Membership
- IEEE Journal of Selected Topics in Signal Processing
- (ICME 2026) 2026 IEEE International Conference on Multimedia and Expo
- IEEE Signal Processing Letters
- Inside Signal Processing Newsletter
- Information for Authors-SPL
- Conference Call for Papers
- Unified EDICS
- Congratulations to Signal Processing Society Members Elevated to Senior Members!
All time:
- Information for Authors
- Submit a Manuscript
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Audio, Speech and Language Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Signal Processing
- Conferences & Events
- IEEE Journal of Selected Topics in Signal Processing
- Information for Authors-SPL
- Conference Call for Papers
- Signal Processing 101
- IEEE Signal Processing Magazine
- Guidelines
Last viewed:
- Deep Unfolding Network for Spatiospectral Image Super-Resolution
- 2025 14th International Symposium on Image and Signal Processing and Analysis (ISPA)
- (ASRU 2025) 2025 IEEE Automatic Speech Recognition and Understanding Workshop
- (ICIP 2025) 2025 IEEE International Conference on Image Processing
- Adaptive Reverberation Absorption Using Non-Stationary Masking Components Detection for Intelligibility Improvement
- SPS Webinar: Rapid, Accurate, and Explainable Video Quality Assessment for User-Generated Content
- IEEE Transactions on Audio, Speech and Language Processing
- IEEE Signal Processing Letters
- Submit a Manuscript
- IEEE Open Journal of Signal Processing
- PhD Position in Computational Imaging
- SPS Scholarship Program
- (ICIP 2026) 2026 IEEE International Conference on Image Processing
- IEEE Transactions on Multimedia
- Winners of the Student Autonomous Underwater Vehicles Challenge Announced
Li, Hongjuan, (The George Washington University),” Privacy Preserving Friend Discoverym in Mobile Social Networks” (2016)
You are here
Newsletter Menu
Newsletter Categories
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
News and Resources for Members of the IEEE Signal Processing Society
Li, Hongjuan, (The George Washington University),” Privacy Preserving Friend Discoverym in Mobile Social Networks” (2016)
Li, Hongjuan, (The George Washington University),” Privacy Preserving Friend Discoverym in Mobile Social Networks” (2016), Advisor: Cheng, Xiuzhen
Mobile social networking has been increasingly popular with the explosive growth of mobile devices. By allowing mobile users to interact with potential friends around the real world, it enables new social interactions as a complement to web-based online social networks. Motivated by this feature, many exciting applications have been developed, yet the challenge of privacy protection is also aroused. This dissertation studies the problem of privacy preserving in mobile social networks. The authors propose different mechanisms for various privacy requirements.
The first proposed algorithm is a secure friend discovery mechanism based on encounter history in mobile social networks, which mainly focuses on the location privacy. By exploring the fact that sharing encounters indicate common activities and interests, the proposed scheme can help people make friends with likeminded strangers nearby. We provide peer-to-peer confidential communications with the location privacy and encounter privacy being strictly preserved. Unlike most existing works that either rely on a trusted centralized server or existing social relationships, the proposed algorithm is designed in an ad-hoc model with no such limitation. As a result, the proposed design is more suitable and more general for mobile social scenarios.
The authors also develop an efficient customized privacy preserving mechanism, which not only protects the privacy of users’ profile, but also establishes a verifiable secure communication channel between matching users. Besides, the initiator has the freedom to set a customized request profile by choosing the interested attributes and giving each attribute a specific value. Moreover, the request profile’s privacy protection level is customized by the initiator according to his/her own privacy requirements. The authors also consider the collusion attacks among unmatched users.
The proposed protocol guarantees only exactly matching users are able to communicate with the initiator securely, while as little as possible information can be obtained by other participants. To increase the matching efficiency, the proposed design adopts the Bloom filter to efficiently exclude most unmatched users. As a result, the proposed design effectively protects the profile privacy and efficiently decreases the computation overhead. The third work for this dissertation explores fine-grained profile matching by associating a user-specific numerical value with each attribute to indicate the level of interest. And the profile similarity is computed with a secure dot-product. While existing studies are mainly focused on leveraging rich cryptography algorithms to prevent privacy leakage, the authors consider a novel cooperative framework by mixing some random noise with the private data to preserve privacy. By carefully tuning the amount of information owned by each party, it is guaranteed that the privacy is effectively preserved while the matching result of two profiles can be cooperatively obtained. After giving an introduction of the basic mechanism, the authors detail two enhanced mechanisms by taking collusion attack and verifiability into consideration. With no expensive encryption algorithms involved, the proposed methods are more practical for real-world applications.
Open Calls
Society News
- Reminder call for Nominations: IEEE Fellow Class of 2017: Deadline 1 March
- Call for Nominations: IEEE Signal Processing Letters Editor-in-Chief
- 2015 IEEE Signal Processing Society Accomplishments
- Member Discounts: International Life Insurance
- vTools Release Announcement: eNotice Express
- Reminder: 2015 Annual Reporting and Rebate Requirements: Due 15 March
- SPS Jobs Marketplace
- Upcoming Distinguished Lectures
- Video of the month: NVIDIA Unveils Supercomputer for Self-driving Cars
- 2015 Conference Best Paper Award for Industry
Education & Resources
- Joint IEEE SPS and EURASIP Summer School on Robust Signal Processing, Rüdesheim (Rhine), Germany, Sept. 19th-24th 2016
- IEEE Meetings, Conferences & Events (MCE) Conference Education Program Webinars: Using mobile apps and IEEE Collabratec to enhance engagement
- IEEE Women in Engineering News: Register Now for 2016 WIE International Leadership Conference
Publications News
Technical Committee News
PhD Theses
SPS Social Media
- IEEE SPS Facebook Page https://www.facebook.com/ieeeSPS
- IEEE SPS X Page https://x.com/IEEEsps
- IEEE SPS Instagram Page https://www.instagram.com/ieeesps/?hl=en
- IEEE SPS LinkedIn Page https://www.linkedin.com/company/ieeesps/
- IEEE SPS YouTube Channel https://www.youtube.com/ieeeSPS
Home | Sitemap | Contact | Accessibility | Nondiscrimination Policy | IEEE Ethics Reporting | IEEE Privacy Policy | Terms | Feedback
© Copyright 2025 IEEE - All rights reserved. Use of this website signifies your agreement to the IEEE Terms and Conditions.
A public charity, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity.