- Our Story
- Publications & Resources
- Publications & Resources
- Publications
- IEEE Signal Processing Magazine
- IEEE Journal of Selected Topics in Signal Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Computational Imaging
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Signal and Information Processing over Networks
- IEEE Transactions on Signal Processing
- IEEE TCI
- IEEE TSIPN
- Data & Challenges
- Submit Manuscript
- Guidelines
- Information for Authors
- Special Issue Deadlines
- Overview Articles
- Top Accessed Articles
- SPS Newsletter
- SigPort
- SPS Resource Center
- Publications FAQ
- Blog
- News
- Dataset Papers
- Conferences & Events
- Community & Involvement
- Professional Development
- For Volunteers
- Information for Authors-OJSP
-
Home
Conferences Events IEEE Signal Processing Magazine IEEE SPL Article IEEE TIFS Article IEEE TMM Article IEEE TSP Article Jobs in Signal Processing Lectures Machine Learning Seasonal Schools Signal Processing News SPM Article SPS Distinguished Lectures SPS Newsletter Article SPS Webinar SPS Webinars SPS Webinar Series Webinar webinars
-
Our Story
What is Signal Processing?
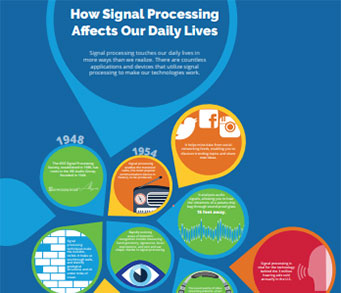
The technology we use, and even rely on, in our everyday lives –computers, radios, video, cell phones – is enabled by signal processing. Learn More » -
Publications & Resources
-
SPS Resources
- Signal Processing Magazine The premier publication of the society.
- SPS Newsletter Monthly updates in Signal Processing
- SPS Resource Center Online library of tutorials, lectures, and presentations.
- SigPort Online repository for reports, papers, and more.
- SPS Feed The latest news, events, and more from the world of Signal Processing.
-
SPS Resources
-
Conferences & Events
-
Community & Involvement
-
Membership
- Join SPS The IEEE Signal Processing Magazine, Conference, Discounts, Awards, Collaborations, and more!
- Chapter Locator Find your local chapter and connect with fellow industry professionals, academics and students
- Women in Signal Processing Networking and engagement opportunities for women across signal processing disciplines
- Students Scholarships, conference discounts, travel grants, SP Cup, VIP Cup, 5-MICC
- Young Professionals Career development opportunities, networking
- Get Involved
-
Technical Committees
- Applied Signal Processing Systems
- Audio and Acoustic Signal Processing
- Bio Imaging and Signal Processing
- Computational Imaging
- Image Video and Multidimensional Signal Processing
- Information Forensics and Security
- Machine Learning for Signal Processing
- Multimedia Signal Processing
- Sensor Array and Multichannel
- Signal Processing for Communication and Networking
- Signal Processing Theory and Methods
- Speech and Language Processing
- Technical Working Groups
- More TC Resources
-
Membership
-
Professional Development
-
Professional Development
- Signal Processing Mentorship Academy (SigMA) Program
- Micro Mentoring Experience Program (MiME)
- Distinguished Lecturer Program
- Distinguished Lecturers
- Distinguished Lecturer Nominations
- Past Lecturers
- Distinguished Industry Speaker Program
- Distinguished Industry Speakers
- Distinguished Industry Speaker Nominations
- Industry Resources
- IEEE Training Materials
- Jobs in Signal Processing: IEEE Job Site
-
Career Resources
- SPS Education Program Educational content in signal processing and related fields.
- Distinguished Lecturer Program Chapters have access to educators and authors in the fields of Signal Processing
- Job Opportunities Signal Processing and Technical Committee specific job opportunities
- Job Submission Form Employers may submit opportunities in the area of Signal Processing.
-
Professional Development
-
For Volunteers
-
For Board & Committee Members
- Board Agenda/Minutes* Agendas, minutes and supporting documentation for Board and Committee Members
- SPS Directory* Directory of volunteers, society and division directory for Board and Committee Members.
- Membership Development Reports* Insight into the Society’s month-over-month and year-over-year growths and declines for Board and Committee Members
-
For Board & Committee Members
Popular Pages
Today's:
- Information for Authors
- (ASRU 2025) 2025 IEEE Automatic Speech Recognition and Understanding Workshop
- IEEE Transactions on Information Forensics and Security
- (ICME 2026) 2026 IEEE International Conference on Multimedia and Expo
- IEEE Transactions on Multimedia
- Submit a Manuscript
- IEEE Signal Processing Letters
- Information for Authors-SPL
- IEEE Transactions on Image Processing
- Submit Your Papers for ICASSP 2026!
- (ICASSP 2026) 2026 IEEE International Conference on Acoustics, Speech, and Signal Processing
- IEEE Journal of Selected Topics in Signal Processing
- Conference Call for Papers
- IEEE JSTSP Special Issue on Advanced AI and Signal Processing for Low-Altitude Wireless Networks
- IEEE Transactions on Audio, Speech and Language Processing
All time:
- Information for Authors
- Submit a Manuscript
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Audio, Speech and Language Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Signal Processing
- Conferences & Events
- IEEE Journal of Selected Topics in Signal Processing
- Information for Authors-SPL
- Conference Call for Papers
- Signal Processing 101
- IEEE Signal Processing Magazine
- Guidelines
Last viewed:
- About SP Letters
- IEEE Signal Processing Letters
- (SAM 2024) 2024 IEEE 13th Sensor Array and Multichannel Signal Processing Workshop
- Information for Authors
- (ISBI 2020) 2020 International Symposium on Biomedical Imaging (ISBI)
- Publications Board
- IEEE Transactions on Signal Processing
- Awards & Submit Award Nomination
- Submit a Manuscript
- SPS Resource Center
- Call for Proposals: IEEE MLSP 2026
- Member Highlight: Archana Venkataraman
- (ASRU 2025) 2025 IEEE Automatic Speech Recognition and Understanding Workshop
- Congratulations to Signal Processing Society Members Elevated to Senior Members!
- SPS-ASI Webinar: Model-Based Deep Learning in Signal Processing and Communications
Kailkhura, Bhavya, Ph.D., Syracuse University, “Distributed inference and learning with Byzantine data” (2017)
You are here
Newsletter Menu
Newsletter Categories
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
News and Resources for Members of the IEEE Signal Processing Society
Kailkhura, Bhavya, Ph.D., Syracuse University, “Distributed inference and learning with Byzantine data” (2017)
Kailkhura, Bhavya, Ph.D., SYRACUSE UNIVERSITY, “Distributed inference and learning with Byzantine data” (2017) Advisor: Varshney, Pramod K.
We are living in an increasingly networked world with sensing networks of varying shapes and sizes: the network often comprises of several tiny devices (or nodes) communicating with each other via different topologies. To make the problem even more complicated, the nodes in the network can be unreliable due to a variety of reasons: noise, faults and attacks, thus, providing corrupted data. Although the area of statistical inference has been an active area of research in the past, distributed learning and inference in a networked setup with potentially unreliable components has only gained attention recently. The emergence of big and dirty data era demands new distributed learning and inference solutions to tackle the problem of inference with corrupted data.
Distributed inference networks (DINs) consist of a group of networked entities which acquire observations regarding a phenomenon of interest (POI), collaborate with other entities in the network by sharing their inference via different topologies to make a global inference. The central goal of this thesis is to analyze the effect of corrupted (or falsified) data on the inference performance of DINs and design robust strategies to ensure reliable overall performance for several practical network architectures. Specifically, the inference (or learning) process can be that of detection or estimation or classification, and the topology of the system can be parallel, hierarchical or fully decentralized (peer to peer).
First, the authors consider the problem of distributed Bayesian detection in the presence of data falsification (or Byzantine) attacks in the parallel topology. Byzantines considered in this thesis are those nodes that are compromised and reprogrammed by an adversary to transmit false information to a centralized fusion center (FC) to degrade detection performance. The authors show that above a certain fraction of Byzantine attackers in the network, the detection scheme becomes completely incapable (or blind) of utilizing the sensor data for detection. When the fraction of Byzantines is not sufficient to blind the FC, the authors also provide closed form expressions for the optimal attacking strategies for the Byzantines that most degrade the detection performance. Optimal attacking strategies in certain cases have the minimax property and, therefore, the knowledge of these strategies has practical significance and can be used to implement a robust detector at the FC.
In several practical situations, parallel topology cannot be implemented due to limiting factors, such as, the FC being outside the communication range of the nodes and limited energy budget of the nodes. In such scenarios, a multi-hop network is employed, where nodes are organized hierarchically into multiple levels (tree networks). Next, the authors study the problem of distributed inference in tree topologies in the presence of Byzantines under several practical scenarios. The authors analytically characterize the effect of Byzantines on the inference performance of the system. The authors also look at the possible counter-measures from the FC’s perspective to protect the network from these Byzantines. These counter-measures are of two kinds: Byzantine identification schemes and Byzantine tolerant schemes. Using learning based techniques, Byzantine identification schemes are designed that learn the identity of Byzantines in the network and use this information to improve system performance. For scenarios where this is not possible, Byzantine tolerant schemes, which use game theory and error-correcting codes, are developed that tolerate the effect of Byzantines while maintaining a reasonably good inference performance in the network.
Going a step further, the authors also consider scenarios where a centralized FC is not available. In such scenarios, a solution is to employ detection approaches which are based on fully distributed consensus algorithms, where all of the nodes exchange information only with their neighbors.
The above considerations highlight the negative effect of the corrupted data on the inference performance. However, it is possible for a system designer to utilize the corrupted data for network’s benefit. Finally, the authors consider the problem of detecting a high dimensional signal based on compressed measurements with secrecy guarantees. The authors consider a scenario where the network operates in the presence of an eavesdropper who wants to discover the state of the nature being monitored by the system. To keep the data secret from the eavesdropper, the authors propose to use cooperating trustworthy nodes that assist the FC by injecting corrupted data in the system to deceive the eavesdropper. The authors also design the system by determining the optimal values of parameters which maximize the detection performance at the FC while ensuring perfect secrecy at the eavesdropper.
Open Calls
| Nomination/Position | Deadline |
|---|---|
| Call for Mentors: 2025 IEEE SPS SigMA Program - Signal Processing Mentorship Academy | 14 September 2025 |
| Last Call for Nominations: Technical Committee Vice Chair and Member Positions | 15 September 2025 |
| Call for Nominations: Technical Committee Vice Chair and Member Positions | 15 September 2025 |
| Submit Your Papers for ICASSP 2026! | 17 September 2025 |
| Call for Nominations: Awards Board, Industry Board and Nominations & Elections Committee | 19 September 2025 |
| Meet the 2025 Candidates: IEEE President-Elect | 1 October 2025 |
| Take Part in the 2025 Low-Resource Audio Codec (LRAC) Challenge | 1 October 2025 |
| Call for proposals: 2027 IEEE Conference on Artificial Intelligence (CAI) | 1 October 2025 |
| Call for Nominations for the SPS Chapter of the Year Award | 15 October 2025 |
| Submit a Proposal for ICASSP 2030 | 31 October 2025 |
| Call for Project Proposals: IEEE SPS SigMA Program - Signal Processing Mentorship Academy | 2 November 2025 |
Member Highlights
Conferences & Events
Technical Committee News
Society News
- IEEE BMC Newsletter – February 2017
- 2017 Member-Driven Initiative
- Reminder: 2016 Annual Reporting and Rebate Requirements: Financial Reporting Due 28 February; Meeting and Officer Reporting Due 15 March
- Upcoming Distinguished Lectures
- Call for Proposals: IEEE ICME 2019, 2020, 2021
- Featured News Around IEEE: IEEE Smart Grid Newsletter
- Job Opportunities in Signal Processing
- Member News: Steve Chen
- IEEE-USA Offers Free e-Books to Members in January and February
- IEEE Launches New 5G Initiative and Seeks Volunteers
- 47 SPS Members Elevated to Fellow
- IEEE Women in Engineering News: WIE ILC 2017, Call for Award Nominations, Scholarship Opportunities
- New Online Submission Process for Geographic Unit Formations
- Call for Nominations: IEEE Medals and Recognitions
- Reminder Call for Nominations: IEEE Fellow Class of 2018: Deadline 1 March
- Give the Gift of IEEE Membership
- Announcing the Latest Innovations for vTools.Events and eNotice
- Member News: Sensors and Sensibility by Vladimir Pavlovic
- Call for Nominations for Editors-in-Chief - Deadline Extended - 24 February
SPS Social Media
- IEEE SPS Facebook Page https://www.facebook.com/ieeeSPS
- IEEE SPS X Page https://x.com/IEEEsps
- IEEE SPS Instagram Page https://www.instagram.com/ieeesps/?hl=en
- IEEE SPS LinkedIn Page https://www.linkedin.com/company/ieeesps/
- IEEE SPS YouTube Channel https://www.youtube.com/ieeeSPS
Home | Sitemap | Contact | Accessibility | Nondiscrimination Policy | IEEE Ethics Reporting | IEEE Privacy Policy | Terms | Feedback
© Copyright 2025 IEEE - All rights reserved. Use of this website signifies your agreement to the IEEE Terms and Conditions.
A public charity, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity.








