- Our Story
- Publications & Resources
- Publications & Resources
- Publications
- IEEE Signal Processing Magazine
- IEEE Journal of Selected Topics in Signal Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Computational Imaging
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Signal and Information Processing over Networks
- IEEE Transactions on Signal Processing
- IEEE TCI
- IEEE TSIPN
- Data & Challenges
- Submit Manuscript
- Guidelines
- Information for Authors
- Special Issue Deadlines
- Overview Articles
- Top Accessed Articles
- SPS Newsletter
- SigPort
- SPS Resource Center
- Publications FAQ
- Blog
- News
- Dataset Papers
- Conferences & Events
- Community & Involvement
- Professional Development
- For Volunteers
- Information for Authors-OJSP
-
Home
Forums12 February 2026 to 13 February 2026Conferences Events IEEE Signal Processing Magazine IEEE SPL Article IEEE TIFS Article IEEE TMM Article IEEE TSP Article Jobs in Signal Processing Lectures Machine Learning Seasonal Schools Signal Processing News SPM Article SPS Distinguished Lectures SPS Newsletter Article SPS Webinar SPS Webinars SPS Webinar Series Webinar webinars
-
Our Story
What is Signal Processing?
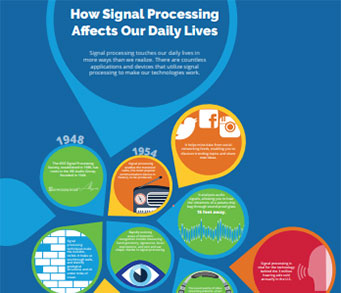
The technology we use, and even rely on, in our everyday lives –computers, radios, video, cell phones – is enabled by signal processing. Learn More » -
Publications & Resources
-
SPS Resources
- Signal Processing Magazine The premier publication of the society.
- SPS Newsletter Monthly updates in Signal Processing
- SPS Resource Center Online library of tutorials, lectures, and presentations.
- SigPort Online repository for reports, papers, and more.
- SPS Feed The latest news, events, and more from the world of Signal Processing.
-
SPS Resources
-
Conferences & Events
-
Community & Involvement
-
Membership
- Join SPS The IEEE Signal Processing Magazine, Conference, Discounts, Awards, Collaborations, and more!
- Chapter Locator Find your local chapter and connect with fellow industry professionals, academics and students
- Women in Signal Processing Networking and engagement opportunities for women across signal processing disciplines
- Students Scholarships, conference discounts, travel grants, SP Cup, VIP Cup, 5-MICC
- Young Professionals Career development opportunities, networking
- Get Involved
-
Technical Committees
- Applied Signal Processing Systems
- Audio and Acoustic Signal Processing
- Bio Imaging and Signal Processing
- Computational Imaging
- Image Video and Multidimensional Signal Processing
- Information Forensics and Security
- Machine Learning for Signal Processing
- Multimedia Signal Processing
- Sensor Array and Multichannel
- Signal Processing for Communication and Networking
- Signal Processing Theory and Methods
- Speech and Language Processing
- Technical Working Groups
- More TC Resources
-
Membership
-
Professional Development
-
Professional Development
- Signal Processing Mentorship Academy (SigMA) Program
- Micro Mentoring Experience Program (MiME)
- Distinguished Lecturer Program
- Distinguished Lecturers
- Distinguished Lecturer Nominations
- Past Lecturers
- Distinguished Industry Speaker Program
- Distinguished Industry Speakers
- Distinguished Industry Speaker Nominations
- Industry Resources
- IEEE Training Materials
- Jobs in Signal Processing: IEEE Job Site
-
Career Resources
- SPS Education Program Educational content in signal processing and related fields.
- Distinguished Lecturer Program Chapters have access to educators and authors in the fields of Signal Processing
- Job Opportunities Signal Processing and Technical Committee specific job opportunities
- Job Submission Form Employers may submit opportunities in the area of Signal Processing.
-
Professional Development
-
For Volunteers
-
For Board & Committee Members
- Board Agenda/Minutes* Agendas, minutes and supporting documentation for Board and Committee Members
- SPS Directory* Directory of volunteers, society and division directory for Board and Committee Members.
- Membership Development Reports* Insight into the Society’s month-over-month and year-over-year growths and declines for Board and Committee Members
-
For Board & Committee Members
Popular Pages
Today's:
- Information for Authors
- (ICME 2026) 2026 IEEE International Conference on Multimedia and Expo
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- Submit a Manuscript
- IEEE Transactions on Multimedia
- Information for Authors-SPL
- Unified EDICS
- Conference Call for Papers
- IEEE Signal Processing Letters
- Editorial Board
- IEEE Transactions on Audio, Speech and Language Processing
- IEEE Open Journal of Signal Processing
- IEEE Transactions on Signal Processing
- IEEE Journal of Selected Topics in Signal Processing
All time:
- Information for Authors
- Submit a Manuscript
- IEEE Transactions on Image Processing
- IEEE Transactions on Information Forensics and Security
- IEEE Transactions on Multimedia
- IEEE Transactions on Audio, Speech and Language Processing
- IEEE Signal Processing Letters
- IEEE Transactions on Signal Processing
- Conferences & Events
- IEEE Journal of Selected Topics in Signal Processing
- Information for Authors-SPL
- Conference Call for Papers
- Signal Processing 101
- IEEE Signal Processing Magazine
- Guidelines
Last viewed:
- (ICME 2026) 2026 IEEE International Conference on Multimedia and Expo
- (AVSS 2025) 2025 IEEE International Conference on Advanced Video and Signal-Based Surveillance
- IEEE Transactions on Image Processing
- Data Science Initiative
- IEEE Transactions on Computational Imaging
- Filter Design for Autoregressive Moving Average Graph Filters
- SPS Scholarship Program
- Information for Authors
- (SPAWC 2026) IEEE 27th International Workshop on Signal Processing and Artificial Intelligence for Wireless Communications
- (ASRU 2025) 2025 IEEE Automatic Speech Recognition and Understanding Workshop
- Editorial Board Nominations
- Member Highlight: Dr. Monika Aggarwal - Professor, IIT, Delhi, India
- Awards & Submit Award Nomination
- Information for Authors-SPL
- Job Opportunities in Signal Processing
Wilamowski, George Christopher. (The George Washington University), “Using Analytical Network Processes to Create Authorization, Authentication, and Accounting Cyber Security Metrics” (2017)
You are here
Newsletter Menu
Newsletter Categories
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
News and Resources for Members of the IEEE Signal Processing Society
Wilamowski, George Christopher. (The George Washington University), “Using Analytical Network Processes to Create Authorization, Authentication, and Accounting Cyber Security Metrics” (2017)
Wilamowski, George Christopher. (The George Washington University), “Using Analytical Network Processes to Create Authorization, Authentication, and Accounting Cyber Security Metrics” (2017) Advisor: Sarkani, Shahram and Mazzuchi, Thomas
Cyber-attacks have escalated, causing decision makers to assess the trade-offs required to protect their organizations from such attacks. The use of benchmarking techniques to reduce cyber security risks would allow decision makers to use both qualitative and quantitative analyses. Systems engineering provides unique insights into the validation of an organization’s criteria for operational objectives through measures of effectiveness for cyber-security decisions.
Decision makers can create cyber-defense strategies by using benchmarking to assess the effectiveness of Authentication, Authorization, and Accounting (AAA) access controls. This dissertation explores the use of the Analytical Network Process (ANP) Multi-Criteria Decision Making (MCDM) model to derive those strategies. A network/access mobile security use case was developed in a generalized application- benchmarking framework. Three communities of interest, the local area network (LAN), wide area network (WAN), and Remote Users, were referenced while demonstrating how to prioritize alternatives within weighted rankings. Subjective judgments carry tremendous weight in the minds of cyber-security decision makers.
Over 500 cyber security Subject Matter Experts (SMEs) completed a survey, giving insights into their expertise and seasoned judgement. They came from a broad cross-section of environments including Military, Government, Nonprofit, and Commercial industries. Using their responses, a generalized application-benchmarking framework was developed that shows how leaders can connect to their technical staffs, thus instantiating cyber defenses that hold the most promise.
The framework consists of four functional areas: (1) Hierarchical Structure; (2) Judgment Dominance with Alternatives; (3) Measures, and (4) Analysis. These four functional areas allow for three composite types: Form, Fit-For-Purpose, and Function to initiate processes and procedures in developing a measure of effectiveness for cyber-security controls. Within the Form composite type, a data parser was used to break the collected raw data into multiple tabulated forms for continued analysis to include an ANP cyber-security controls diagram. The Fit-For-Purpose composite analyzed the data in relation to data normalization, chi-square test for independence, residual plotting, the general linear model (GLM), geometric mean, and Cronbach’s alpha. Once the data were analyzed, the information was refined within the Function composite and subjected to pairwise comparisons within the ANP models for continued development of benchmarking scorecards. The result of that process was a security rating for LAN, WAN, and remote-user configurations.
In the final analysis, it was determined that a generalized application-benchmarking framework can be employed to derive Measures of Effectiveness (MOEs) based on SME preferences for security controls. The security measures formulated from the model allowed them to be given weighted scores and to be ranked from the development of ANP scorecards for each industry type. The scorecards and rankings allow industry security managers to compare their own rankings against the benchmarked scorecards to increase the effectiveness of cyber-security controls within their organizations.
Open Calls
| Nomination/Position | Deadline |
|---|---|
| Call for Nominations for the SPS Chapter of the Year Award | 15 October 2025 |
| Call for Papers for 2026 LRAC Workshop | 22 October 2025 |
| Submit Your 2026 ICASSP Workshop Paper | 22 October 2025 |
| Submit a Proposal for ICASSP 2030 | 31 October 2025 |
| Call for Project Proposals: IEEE SPS SigMA Program - Signal Processing Mentorship Academy | 2 November 2025 |
| Submit Your Proposals for 2026 Member-Driven Initiatives | 21 November 2025 |
| IEEE Signal Processing Society Annual Election Opens on 17 October | 4 December 2025 |
Member Highlights
Conferences & Events
Technical Committee News
Society News
- IEEE BMC Newsletter – February 2017
- 2017 Member-Driven Initiative
- Reminder: 2016 Annual Reporting and Rebate Requirements: Financial Reporting Due 28 February; Meeting and Officer Reporting Due 15 March
- Upcoming Distinguished Lectures
- Call for Proposals: IEEE ICME 2019, 2020, 2021
- Featured News Around IEEE: IEEE Smart Grid Newsletter
- Job Opportunities in Signal Processing
- Member News: Steve Chen
- IEEE-USA Offers Free e-Books to Members in January and February
- IEEE Launches New 5G Initiative and Seeks Volunteers
- 47 SPS Members Elevated to Fellow
- IEEE Women in Engineering News: WIE ILC 2017, Call for Award Nominations, Scholarship Opportunities
- New Online Submission Process for Geographic Unit Formations
- Call for Nominations: IEEE Medals and Recognitions
- Reminder Call for Nominations: IEEE Fellow Class of 2018: Deadline 1 March
- Give the Gift of IEEE Membership
- Announcing the Latest Innovations for vTools.Events and eNotice
- Member News: Sensors and Sensibility by Vladimir Pavlovic
- Call for Nominations for Editors-in-Chief - Deadline Extended - 24 February
SPS Social Media
- IEEE SPS Facebook Page https://www.facebook.com/ieeeSPS
- IEEE SPS X Page https://x.com/IEEEsps
- IEEE SPS Instagram Page https://www.instagram.com/ieeesps/?hl=en
- IEEE SPS LinkedIn Page https://www.linkedin.com/company/ieeesps/
- IEEE SPS YouTube Channel https://www.youtube.com/ieeeSPS
Home | Sitemap | Contact | Accessibility | Nondiscrimination Policy | IEEE Ethics Reporting | IEEE Privacy Policy | Terms | Feedback
© Copyright 2025 IEEE - All rights reserved. Use of this website signifies your agreement to the IEEE Terms and Conditions.
A public charity, IEEE is the world's largest technical professional organization dedicated to advancing technology for the benefit of humanity.