SPS Feed
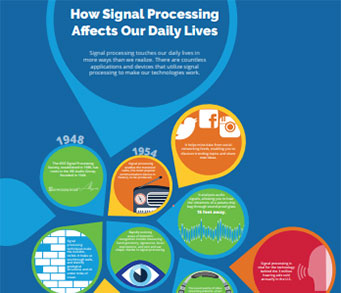
Top Reasons to Join SPS Today!
1. IEEE Signal Processing Magazine
2. Signal Processing Digital Library*
3. Inside Signal Processing Newsletter
4. SPS Resource Center
5. Career advancement & recognition
6. Discounts on conferences and publications
7. Professional networking
8. Communities for students, young professionals, and women
9. Volunteer opportunities
10. Coming soon! PDH/CEU credits
Click here to learn more.
The Latest News, Articles, and Events in Signal Processing
Lecture Date: November 18, 2019
Chapter: Chile
Chapter Chair: Nestor Becerra Yoma
Topic: Data Fusion and Analysis Through Matrix and Tensor
Factorizations: Uniqueness, Diversity and Applications
September 22-25, 2020
NOTE: AVSS 2020 has been postponed to 2021
Location: Washington, DC, USA
January 19-22, 2021
NOTE: Location changed to--Virtual Conference
Lecture Date: November 8, 2019
Chapter: Central Indiana
Chapter Chair: John Mott
Topic: Privacy-Preserving Localization and Recognition of Human Activities
Lecture Date: December 6, 2019
Chapter: Rio de Janeiro
Chapter Chair: Markus V. Lima
Topic: Optimal Multichannel Signal Enhancement
Audio-Visual Voice Activity Detection Using Deep Neural Networks
Lecture Date: December 4-5, 2019
Chapter: South Brazil
Chapter Chair: Vanessa Testoni
Topic: Audio-Visual Voice Activity Detection Using Deep Neural Networks
Lecture Date: December 2-3, 2019
Chapter: Chile
Chapter Chair: Nestor B. Yoma
Topic: Optimal Multichannel Signal Enhancement
Audio-Visual Voice Activity Detection Using Deep Neural Networks
Imagine sitting in a room where every individual is able to read every other individual’s mind. Would you lose your mind? We are living in an age where many of us have already surrendered our personal privacy to online interfaces either knowingly or by deceptive means.
Today, many devices (e.g., cars and other vehicles) we operate for various tasks (e.g., to go from place A to place B) are changing: in the past, they were characterized by a body and control actuators that allowed us to perform these tasks. These days, they are not simply passive recipients of our instructions;
This article examines the problem of interference in automotive radar. Different types of automotive radar as well as mechanisms and characteristics of interference and the effects of interference on radar system performance are described. The interference-to-noise ratio (INR) at the output of a detector is a measure of the susceptibility of a radar to interference. The INR is derived from different types of interfering and victim radars and depends on the location of both as well as parameters such as transmit power, antenna gain, and bandwidth.
The anniversary of a number of significant signal processing algorithms from the 1960s, including the least mean square algorithm and the Kalman filter, provided an opportunity at ICASSP 2019 to reflect on the links between education and innovation. This led ultimately to the proposal of some special sessions as well a panel session that would provide some insight, via a historical perspective, consideration of the current status, and an assessment of the emerging educational future.
The world is moving faster, and signal processing is helping to lead the way, making mobile technologies faster, safer, and more functional on land and even under the sea. At the Massachusetts Institute of Technology (MIT), engineers have created an algorithm that allows autonomous underwater vehicles (AUVs) to weigh the risks and potential rewards of exploring unknown deep-sea sites in real time.
One of the main items of feedback during our recent IEEE Periodicals Review and Advisory Committee (PRAC) meeting was that IEEE Signal Processing Magazine (SPM) rejected too many feature article white papers as being “out of scope.” In this editorial, I attempt to outline the key features of a good feature article.
Lecture Date: October 18, 2019
Chapter: Twin Cities
Chapter Chair: Tao Zhang
Topic: Recent advancements in google speech technologies

We are looking to hire a motivated post-doc to work on machine learning and data analytics in signal processing. The candidate must have a strong background in machine learning, AI, signal processing, optimization methods, probability, and statistics. The candidate must have a Ph.D. in relevant fields.
Required:

About the position:
We have a vacancy for a PhD Research Fellow position at the Department of Electronic Systems (IES). The PhD position is for up to 4 years with 25% work assignments for NTNU IES.
Job description:
January 6-9, 2020
Early Registration Deadline: December 30, 2019
Location: Chile
Website
Pages
SPS Social Media
- IEEE SPS Facebook Page https://www.facebook.com/ieeeSPS
- IEEE SPS X Page https://x.com/IEEEsps
- IEEE SPS Instagram Page https://www.instagram.com/ieeesps/?hl=en
- IEEE SPS LinkedIn Page https://www.linkedin.com/company/ieeesps/
- IEEE SPS YouTube Channel https://www.youtube.com/ieeeSPS